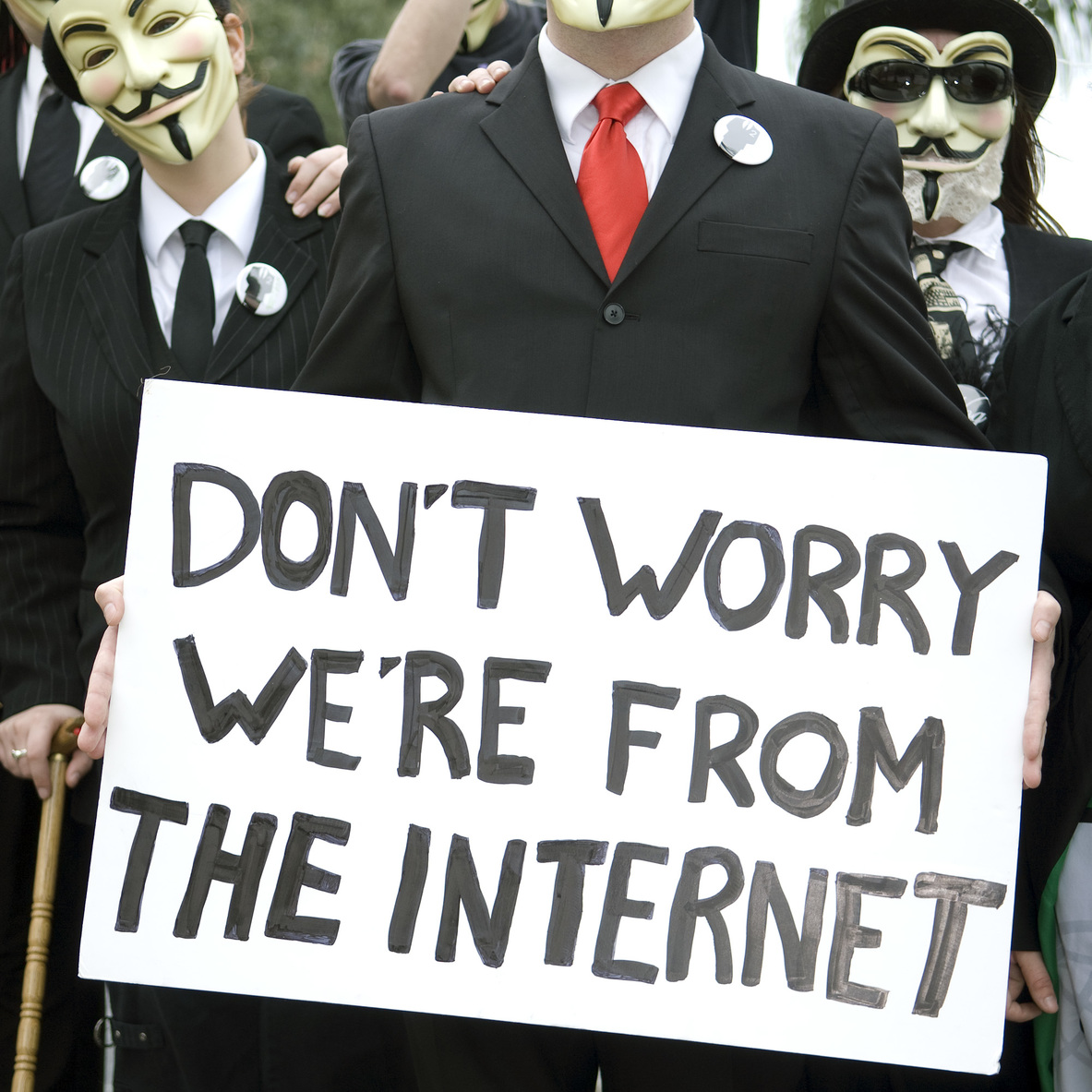
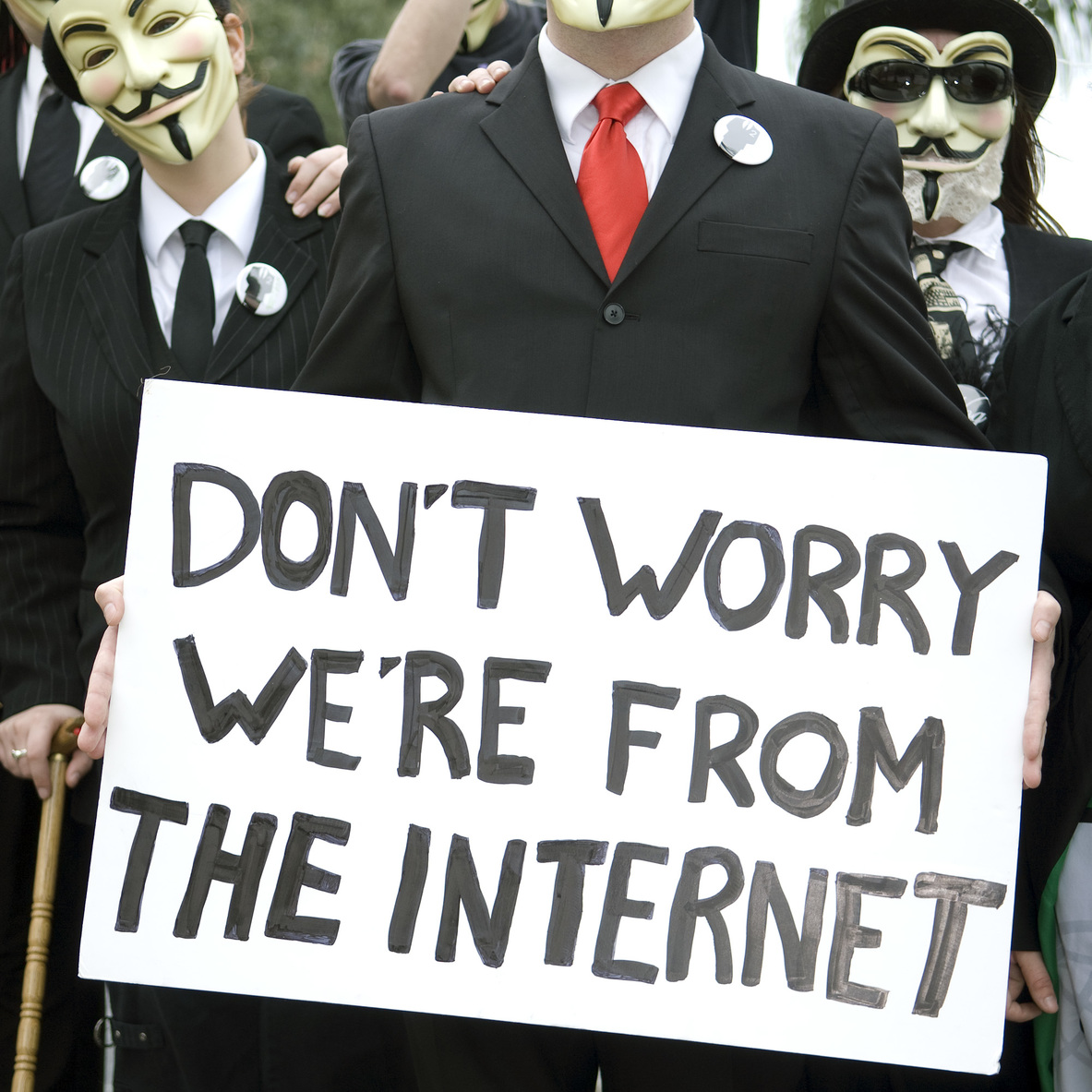
We’re all familiar with the constant barrage of leaks that are released on a daily basis and that have so much potential power that they could topple governments, force important people to resign, drive businesses into bankruptcy and so on. Up until recently, most of the reveals were made by highly competent actors – be them state officials themselves or military personnel – but the appearance of Wikileaks proved how truly powerful this instrument is in the hands of private individuals or organisations.
The recent US Presidential Election clearly pointed out that the importance of exposing formerly political classified intel about an opponent is no longer in the hands of
oppo-researchers that have ties with a certain political campaign – that era is completely over. The internet has brought us a worldwide channel of distribution of important material that could potentially change the future that we know it and more importantly, it has brought us a new actor on the geopolitical stage: the anonymous activist.
Let’s take for example the recent case that is unfolding in Sweden: sensitive personal data of millions of Swedish transporters, along with the nation’s military secrets have been leaked from the Swedish Transport Agency (
Transportstyrelsen) after the agency outsourced the deal to IBM Czech Republic and IBM Romania without any formal consent from the Swedish Security apparatus – the data breach supposedly exposes names, photos and home addresses of millions of Swedish citizens, including military personnel (Swedish Air Force fighter pilots; military installations) and sensitive Police data (suspect names, names of people involved with the witness relocation programme etc.)
A simple IT maintenance contract to manage and outsource the databases and networks of the Swedish Transport Agency has led to one of the worst governmental information security disasters in modern history.
[caption id="attachment_1382" align="aligncenter" width="1000"]

[Sweden's Prime Minister Stefan Lofven speaks during a press conference in Stockholm, Monday, July 24, 2017. Sweden's prime minister says a security leak in the transport agency two years ago was "a disaster," but it's unclear what damage it may have caused. Lofven says the data leak was revealed after security police investigated the outsourcing of services by the Swedish Transport Agency and found IT workers in other countries, including the Czech Republic, were not given normal security checks. (Stina Stjernkvist/TT News Agency via AP)][/caption]Another such case might be that of the British Political PR Firm
Bell Pottinger, covered by Open Source Investigation a couple of weeks ago [link here].
Bell Pottinger came under intense scrutiny after various sources leaked out information that the British firm was spreading racial discontent in South Africa, as per their work for the influential South African Gupta family. The „#
GuptaLeaks” – as it became known in South African newspapers, showed how an influential family tried to stir racial conflict in order to capitalize on it in the next Presidential election.
All of the leaks came from undisclosed sources that shared their info with local newspapers and via the use of the internet.

We all know about the DNC (Democratic National Committee) e-mail leaks that were published on July 22, 2016 by Wikileaks – right in the middle of the US Presidential Elections. The information leaked contained 19.562 e-mails and 8.034 attachments from the DNC – it included e-mails from seven key DNC staff members, including DNC chair Debbie Wasserman Schultz, DNC CEO Amy Dacey, Communications Director Luis Mirinda or Hillary Clinton’s Chief of Staff John Podesta. The importance of these leaks is that they impacted the US Presidential campaign a lot as they clearly showed the corruption of the current political establishment, which in turn caused a lot of people to rethink their votes or to not vote at all. Moreover, the leaks included personal information about the donors of the Democratic Party, including credit card and Social Security numbers, and they also contained DNC’s interactions with the media and Hillary Clinton’s and Bernie Sander’s campaigns for the Democratic Primaries.
Wikileaks never revealed its source for the leaks. A couple of days after the entire scandal broke off, a self-styled hacker going by the name of Guccifer 2.0 claimed responsibility for the attack. However, to this day the real identification of the perpetrator was never found, even if the FBI and several US intelligence agencies investigated the hack.

One of the most important examples of how powerful leaks can truly be is the case of the „
Panama Papers”, also known as
#PanamaGate. On April 15, 2016, 11.5 million documents that detailed financial and attorney-client information for more than 214.488 offshore entities were leaked on the internet, triggering a massive outcry from the civil society, given the fact that there were a lot of public officials involved in the scandal. The documents contained personal financial information about wealthy individuals and politicians that had previously been kept private from the public, with many leading to discovery of fraud, tax evasion, evasion of international sanctions and other illegal purposes. The whole ordeal prompted a massive wave of protests across the world, with many state officials resigning from their posts and many public individuals being put into an awkward situation.
The Panama Leaks were orchestrated by an anonymous whistleblower who leaked the documents to German journalist Bastian Obermayer (
Suddeutsche Zeitung newspaper) – the leaker remained unknown and cited his actions as necessary because “… I understood enough about their contents to realise the scale of the injustices they described”
[caption id="attachment_1385" align="aligncenter" width="4000"]
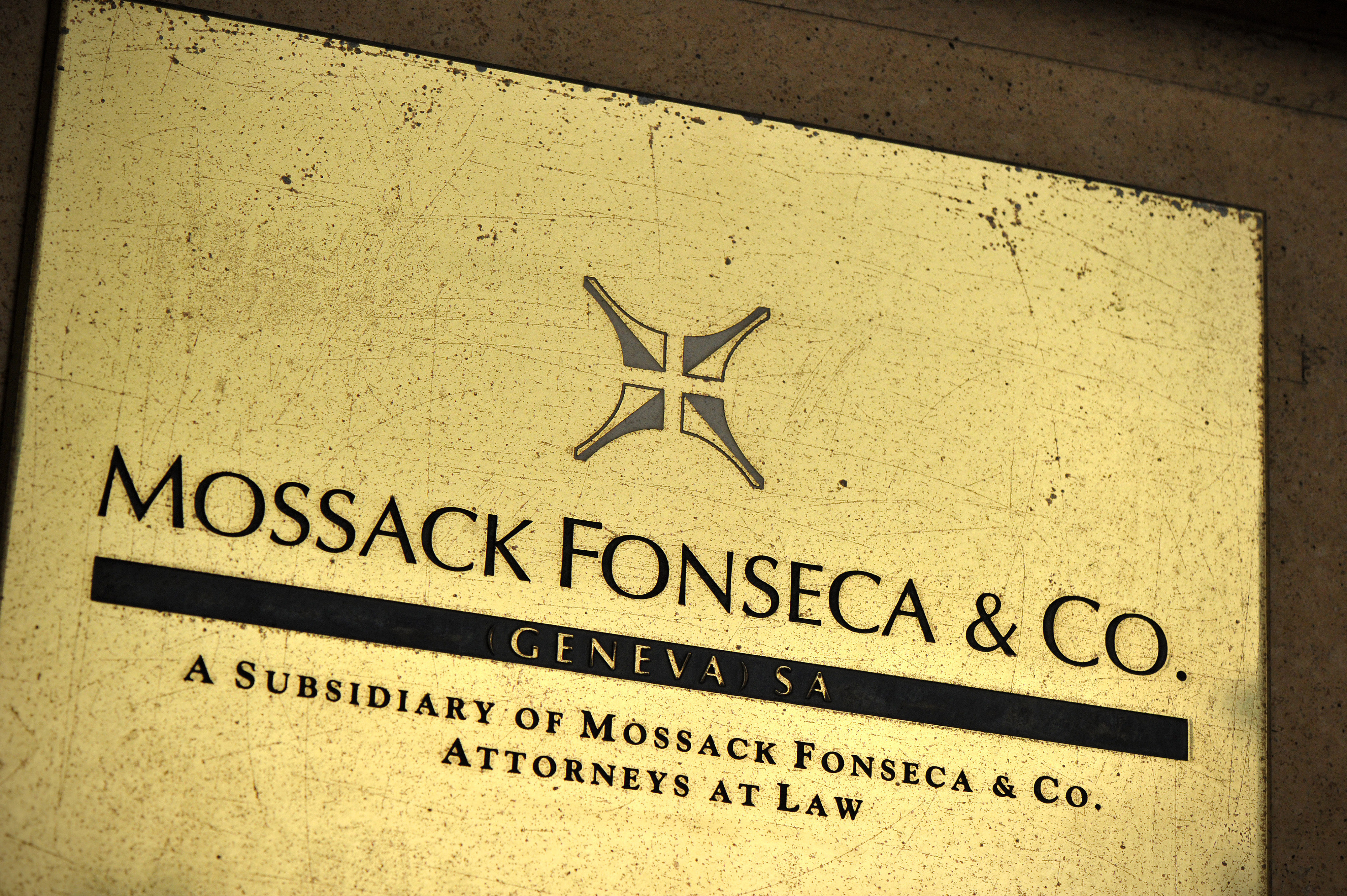
[GENEVA, SWITZERLAND - APRIL 05: A detail of the Mossack Fonseca Geneva office plate on April 5, 2016 in Geneva, Switzerland. 11.5m files anonymously leaked from the database of the world's fourth biggest offshore law firm, Mossack Fonseca, referred to as the 'Panama Papers,' indicates possible secret offshore dealings from world leaders and celebrities. (Photo by Pxl8/Getty Images)][/caption]As we can see, this whole phenomenon is unfolding before our eyes in an increased matter and it will soon become, if it hasn’t already, a massive tool used by virtually all actors involved on the geopolitical scene. Foreign governments, online activists, hackers, private individuals – all of them can now have an open platform on which they can freely distribute sensitive information that could potentially have a large impact if marketed correctly to the general public. The internet has made it us all equal in this regard, as it has allowed us to spread the truth and malicious content on a massive scale, both of which can advance our goals if managed properly.
The future is now and the current political system is just realizing the importance of the internet in the long term. Up until now,
oppo-research was distributed via conventional media outlets, – such as TV, radio, outdoor advertising – outlets that could reach a certain amount of people and cause a stir. Nowadays, all it takes is to fire up a laptop, connect to a public Wi-Fi network and send a couple of well-placed e-mails to a couple of well-connected people: the moment the information hits the web, the wildfire cannot be stopped.
We should get used to the leaks –
they’re here to stay.
 Let’s take for example the recent case that is unfolding in Sweden: sensitive personal data of millions of Swedish transporters, along with the nation’s military secrets have been leaked from the Swedish Transport Agency (Transportstyrelsen) after the agency outsourced the deal to IBM Czech Republic and IBM Romania without any formal consent from the Swedish Security apparatus – the data breach supposedly exposes names, photos and home addresses of millions of Swedish citizens, including military personnel (Swedish Air Force fighter pilots; military installations) and sensitive Police data (suspect names, names of people involved with the witness relocation programme etc.)
A simple IT maintenance contract to manage and outsource the databases and networks of the Swedish Transport Agency has led to one of the worst governmental information security disasters in modern history.
[caption id="attachment_1382" align="aligncenter" width="1000"]
Let’s take for example the recent case that is unfolding in Sweden: sensitive personal data of millions of Swedish transporters, along with the nation’s military secrets have been leaked from the Swedish Transport Agency (Transportstyrelsen) after the agency outsourced the deal to IBM Czech Republic and IBM Romania without any formal consent from the Swedish Security apparatus – the data breach supposedly exposes names, photos and home addresses of millions of Swedish citizens, including military personnel (Swedish Air Force fighter pilots; military installations) and sensitive Police data (suspect names, names of people involved with the witness relocation programme etc.)
A simple IT maintenance contract to manage and outsource the databases and networks of the Swedish Transport Agency has led to one of the worst governmental information security disasters in modern history.
[caption id="attachment_1382" align="aligncenter" width="1000"] [Sweden's Prime Minister Stefan Lofven speaks during a press conference in Stockholm, Monday, July 24, 2017. Sweden's prime minister says a security leak in the transport agency two years ago was "a disaster," but it's unclear what damage it may have caused. Lofven says the data leak was revealed after security police investigated the outsourcing of services by the Swedish Transport Agency and found IT workers in other countries, including the Czech Republic, were not given normal security checks. (Stina Stjernkvist/TT News Agency via AP)][/caption]Another such case might be that of the British Political PR Firm Bell Pottinger, covered by Open Source Investigation a couple of weeks ago [link here]. Bell Pottinger came under intense scrutiny after various sources leaked out information that the British firm was spreading racial discontent in South Africa, as per their work for the influential South African Gupta family. The „#GuptaLeaks” – as it became known in South African newspapers, showed how an influential family tried to stir racial conflict in order to capitalize on it in the next Presidential election.
All of the leaks came from undisclosed sources that shared their info with local newspapers and via the use of the internet.
[Sweden's Prime Minister Stefan Lofven speaks during a press conference in Stockholm, Monday, July 24, 2017. Sweden's prime minister says a security leak in the transport agency two years ago was "a disaster," but it's unclear what damage it may have caused. Lofven says the data leak was revealed after security police investigated the outsourcing of services by the Swedish Transport Agency and found IT workers in other countries, including the Czech Republic, were not given normal security checks. (Stina Stjernkvist/TT News Agency via AP)][/caption]Another such case might be that of the British Political PR Firm Bell Pottinger, covered by Open Source Investigation a couple of weeks ago [link here]. Bell Pottinger came under intense scrutiny after various sources leaked out information that the British firm was spreading racial discontent in South Africa, as per their work for the influential South African Gupta family. The „#GuptaLeaks” – as it became known in South African newspapers, showed how an influential family tried to stir racial conflict in order to capitalize on it in the next Presidential election.
All of the leaks came from undisclosed sources that shared their info with local newspapers and via the use of the internet.
 We all know about the DNC (Democratic National Committee) e-mail leaks that were published on July 22, 2016 by Wikileaks – right in the middle of the US Presidential Elections. The information leaked contained 19.562 e-mails and 8.034 attachments from the DNC – it included e-mails from seven key DNC staff members, including DNC chair Debbie Wasserman Schultz, DNC CEO Amy Dacey, Communications Director Luis Mirinda or Hillary Clinton’s Chief of Staff John Podesta. The importance of these leaks is that they impacted the US Presidential campaign a lot as they clearly showed the corruption of the current political establishment, which in turn caused a lot of people to rethink their votes or to not vote at all. Moreover, the leaks included personal information about the donors of the Democratic Party, including credit card and Social Security numbers, and they also contained DNC’s interactions with the media and Hillary Clinton’s and Bernie Sander’s campaigns for the Democratic Primaries.
Wikileaks never revealed its source for the leaks. A couple of days after the entire scandal broke off, a self-styled hacker going by the name of Guccifer 2.0 claimed responsibility for the attack. However, to this day the real identification of the perpetrator was never found, even if the FBI and several US intelligence agencies investigated the hack.
We all know about the DNC (Democratic National Committee) e-mail leaks that were published on July 22, 2016 by Wikileaks – right in the middle of the US Presidential Elections. The information leaked contained 19.562 e-mails and 8.034 attachments from the DNC – it included e-mails from seven key DNC staff members, including DNC chair Debbie Wasserman Schultz, DNC CEO Amy Dacey, Communications Director Luis Mirinda or Hillary Clinton’s Chief of Staff John Podesta. The importance of these leaks is that they impacted the US Presidential campaign a lot as they clearly showed the corruption of the current political establishment, which in turn caused a lot of people to rethink their votes or to not vote at all. Moreover, the leaks included personal information about the donors of the Democratic Party, including credit card and Social Security numbers, and they also contained DNC’s interactions with the media and Hillary Clinton’s and Bernie Sander’s campaigns for the Democratic Primaries.
Wikileaks never revealed its source for the leaks. A couple of days after the entire scandal broke off, a self-styled hacker going by the name of Guccifer 2.0 claimed responsibility for the attack. However, to this day the real identification of the perpetrator was never found, even if the FBI and several US intelligence agencies investigated the hack.
 One of the most important examples of how powerful leaks can truly be is the case of the „Panama Papers”, also known as #PanamaGate. On April 15, 2016, 11.5 million documents that detailed financial and attorney-client information for more than 214.488 offshore entities were leaked on the internet, triggering a massive outcry from the civil society, given the fact that there were a lot of public officials involved in the scandal. The documents contained personal financial information about wealthy individuals and politicians that had previously been kept private from the public, with many leading to discovery of fraud, tax evasion, evasion of international sanctions and other illegal purposes. The whole ordeal prompted a massive wave of protests across the world, with many state officials resigning from their posts and many public individuals being put into an awkward situation.
The Panama Leaks were orchestrated by an anonymous whistleblower who leaked the documents to German journalist Bastian Obermayer (Suddeutsche Zeitung newspaper) – the leaker remained unknown and cited his actions as necessary because “… I understood enough about their contents to realise the scale of the injustices they described”
[caption id="attachment_1385" align="aligncenter" width="4000"]
One of the most important examples of how powerful leaks can truly be is the case of the „Panama Papers”, also known as #PanamaGate. On April 15, 2016, 11.5 million documents that detailed financial and attorney-client information for more than 214.488 offshore entities were leaked on the internet, triggering a massive outcry from the civil society, given the fact that there were a lot of public officials involved in the scandal. The documents contained personal financial information about wealthy individuals and politicians that had previously been kept private from the public, with many leading to discovery of fraud, tax evasion, evasion of international sanctions and other illegal purposes. The whole ordeal prompted a massive wave of protests across the world, with many state officials resigning from their posts and many public individuals being put into an awkward situation.
The Panama Leaks were orchestrated by an anonymous whistleblower who leaked the documents to German journalist Bastian Obermayer (Suddeutsche Zeitung newspaper) – the leaker remained unknown and cited his actions as necessary because “… I understood enough about their contents to realise the scale of the injustices they described”
[caption id="attachment_1385" align="aligncenter" width="4000"]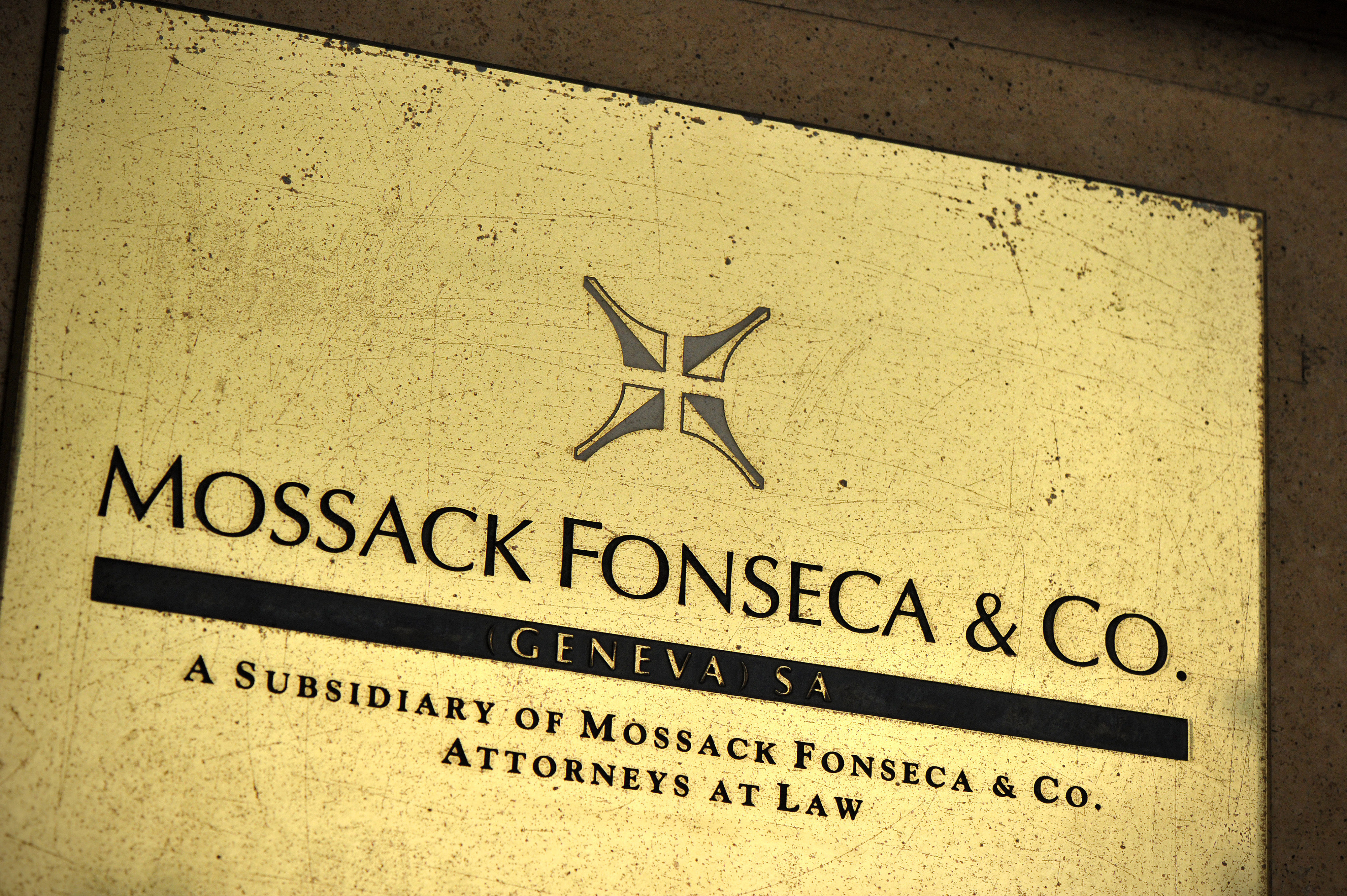 [GENEVA, SWITZERLAND - APRIL 05: A detail of the Mossack Fonseca Geneva office plate on April 5, 2016 in Geneva, Switzerland. 11.5m files anonymously leaked from the database of the world's fourth biggest offshore law firm, Mossack Fonseca, referred to as the 'Panama Papers,' indicates possible secret offshore dealings from world leaders and celebrities. (Photo by Pxl8/Getty Images)][/caption]As we can see, this whole phenomenon is unfolding before our eyes in an increased matter and it will soon become, if it hasn’t already, a massive tool used by virtually all actors involved on the geopolitical scene. Foreign governments, online activists, hackers, private individuals – all of them can now have an open platform on which they can freely distribute sensitive information that could potentially have a large impact if marketed correctly to the general public. The internet has made it us all equal in this regard, as it has allowed us to spread the truth and malicious content on a massive scale, both of which can advance our goals if managed properly.
The future is now and the current political system is just realizing the importance of the internet in the long term. Up until now, oppo-research was distributed via conventional media outlets, – such as TV, radio, outdoor advertising – outlets that could reach a certain amount of people and cause a stir. Nowadays, all it takes is to fire up a laptop, connect to a public Wi-Fi network and send a couple of well-placed e-mails to a couple of well-connected people: the moment the information hits the web, the wildfire cannot be stopped.
We should get used to the leaks – they’re here to stay.
[GENEVA, SWITZERLAND - APRIL 05: A detail of the Mossack Fonseca Geneva office plate on April 5, 2016 in Geneva, Switzerland. 11.5m files anonymously leaked from the database of the world's fourth biggest offshore law firm, Mossack Fonseca, referred to as the 'Panama Papers,' indicates possible secret offshore dealings from world leaders and celebrities. (Photo by Pxl8/Getty Images)][/caption]As we can see, this whole phenomenon is unfolding before our eyes in an increased matter and it will soon become, if it hasn’t already, a massive tool used by virtually all actors involved on the geopolitical scene. Foreign governments, online activists, hackers, private individuals – all of them can now have an open platform on which they can freely distribute sensitive information that could potentially have a large impact if marketed correctly to the general public. The internet has made it us all equal in this regard, as it has allowed us to spread the truth and malicious content on a massive scale, both of which can advance our goals if managed properly.
The future is now and the current political system is just realizing the importance of the internet in the long term. Up until now, oppo-research was distributed via conventional media outlets, – such as TV, radio, outdoor advertising – outlets that could reach a certain amount of people and cause a stir. Nowadays, all it takes is to fire up a laptop, connect to a public Wi-Fi network and send a couple of well-placed e-mails to a couple of well-connected people: the moment the information hits the web, the wildfire cannot be stopped.
We should get used to the leaks – they’re here to stay.









Trackbacks and Pingbacks